$292 Million DeFi Heist Sends Shockwaves Through KelpDAO, Aave, and Arbitrum

A massive exploit targeting the decentralized finance protocol KelpDAO has thrown the entire DeFi ecosystem into turmoil. The attack resulted in the theft of approximately $292 million and carries far-reaching consequences for the lending protocol Aave, the blockchain network Arbitrum, and countless users. While the hackers have already begun laundering the stolen funds, affected protocols are scrambling to limit the damage.
The Attack: How the Exploit Worked
At the center of the attack is rsETH, a so-called liquid restaking token issued by KelpDAO. To transfer rsETH between different blockchains, the protocol relies on a bridge mechanism: tokens are locked on a source chain while corresponding copies are minted on the destination chain.
An attacker exploited a vulnerability in this system by crafting a fraudulent transfer message that was accepted as valid. The tokens were never actually deducted from the sending chain. Instead, 116,500 rsETH were effectively minted without backing and released from the Ethereum-side bridge.
The vulnerability lay in the way KelpDAO verified cross-chain messages via the messaging protocol LayerZero. LayerZero itself was not directly hacked, but its messaging layer enabled flawed assumptions in KelpDAO’s validation logic.
KelpDAO rejected this criticism, stating that the 1-of-1 DVN configuration of LayerZero had been shipped as a default setting. This sparked a public dispute over responsibility between the two protocols.
Aave: Up to $230 Million in Potential Losses
Rather than immediately selling the stolen tokens, the attacker used 89,567 rsETH as collateral on Aave and borrowed approximately $190 million in ETH and related assets on Ethereum and Arbitrum. Since the deposited collateral was effectively unbacked, Aave now faces significant losses from so-called “bad debt” — debt that is not fully collateralized.
Aave Labs responded swiftly: within a matter of hours, rsETH markets were frozen across all deployments, loan-to-value ratios were set to zero, and new borrowing against rsETH was halted.
A joint report by Aave Labs and service provider LlamaRisk outlines two possible scenarios for the final extent of the damage:
| Scenario | Description | Estimated Loss for Aave |
|---|---|---|
| Scenario A | Losses are distributed across all rsETH holders (approx. 15% loss in token value) | approx. $123 million |
| Scenario B | Losses are confined to Layer 2 networks such as Arbitrum and Mantle | up to $230 million |
Which scenario materializes depends largely on how KelpDAO distributes the losses internally. An official decision on this has yet to be made. According to the report, the Aave DAO treasury holds approximately $181 million in assets, and discussions are underway with ecosystem participants regarding possible compensation measures.
The uncertainty surrounding the incident triggered a massive capital outflow: approximately $6 billion in total value locked (TVL) was withdrawn from Aave following the exploit, as users reassessed the risk within the interconnected DeFi infrastructure.
Arbitrum Freezes Stolen Funds
The Layer 2 network Arbitrum responded with an unusual measure: the Arbitrum Security Council froze 30,766 ETH worth approximately $71.1 million that were held in an address linked to the exploit on Arbitrum One. The funds were transferred to an intermediary, locked wallet.
“The Security Council acted in coordination with law enforcement regarding the identity of the attacker, while consistently weighing its commitment to the security and integrity of the Arbitrum community against any impact on other users or applications.”
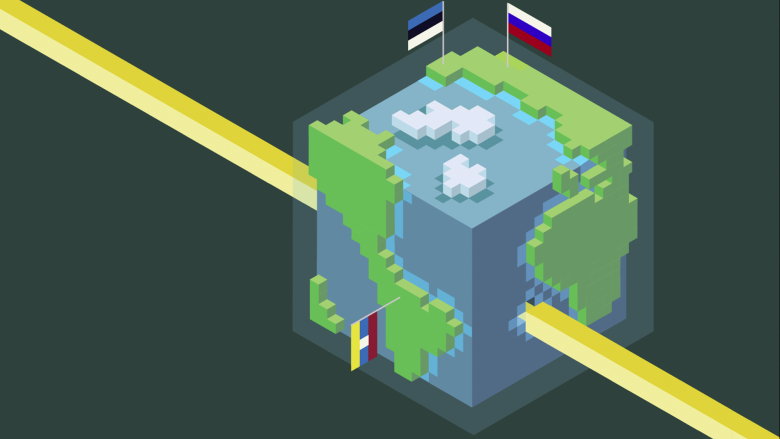
Arbitrum emphasized that the action had no effect on other chain states or regular users. The frozen funds can only be moved through a further resolution by Arbitrum governance. Preliminary findings from LayerZero suggest that the attack may be linked to the North Korean hacker group Lazarus.
Money Laundering: Hackers Cover Their Tracks
In parallel with containment efforts, the hackers have already begun laundering the stolen funds. On-chain investigator ZachXBT and data from blockchain analytics firm Arkham show that the wallet controlling the exploit proceeds executed two transfers of $117 million and $58 million on the Ethereum blockchain on Tuesday.
The obfuscation strategy involves several methods:
- Approximately $1.5 million was bridged from Ethereum to Bitcoin via Thorchain, a protocol previously used by the Lazarus Group for money laundering.
- An additional approximately $78,000 was routed through the privacy protocol Umbra.
- Cross-chain routing and privacy tools are being used to distribute the funds across multiple addresses and networks.
Experts classify this approach as the classic “layering” phase of money laundering, in which funds are moved through multiple intermediate steps to obscure their origin. Arbitrum’s freezing of the $71 million could increase pressure on the attackers to move the remaining funds even more quickly.